Technical Specifications
Compare the feature set of Sophos’s various endpoint products to protect your clients. Not sure which protection best suits your business? We advise you free of charge and completely without obligation.

Seqrite Endpoint Cloud Advanced, coupled with a 1-year subscription, delivers an elevated standard of cybersecurity for your business, providing advanced threat protection and comprehensive endpoint security. Elevate your defense strategy with this cutting-edge solution that combines real-time threat intelligence, cloud-based security, and centralized management for a robust and proactive approach to safeguarding your digital assets.
Pinnacle Studio 26 (Standard) is one of the most popular video editing software. It is well accepted for video editing needs by both hobbyists as well as professional’s across the globe.
In terms of price, this software is much affordable than other video editing software’s, people who buy Pinnacle Studio 26 online can get more advantage because it has a more comprehensive interface and features that make it more impressive. Now, we can customize video creation with the help of dynamic video masking. It provides incredible effects, enhancements, and layering templates. Besides this, with Pinnacle Studio 26, we can do a lot of transformations. Even, we can also transform each section of the frame freely and independently. Furthermore, the latest update has significantly improved the masking tool. And, the Smart Edge tool has a lot of adjustment options that allow you to select and mask the object in any video clip with ease.
With the new title editor in Pinnacle Studio 26, the text graphic options have been greatly expanded. If you buy Pinnacle Studio 26 (Standard) online in India you can edit titles directly in the main video preview, which is a nice improvement over having to open a separate window previously. The degree of control over the titles is astounding. You can use keyframes to not only animate your names but also to add animation to particular words or letters within a title. You can animate graphics with your names, such as a lower thirds box to frame a caption, and you can apply and sync a light source with 3D title editing.
Moreover, you can upgrade your editing control over video clips, pictures, and backgrounds with the latest keyframing tools. Yet, this software provides you with in-depth keyframing controls. It is really helpful in creating stunning video creations or projects with precise sizes and positions.
If you choose to buy Pinnacle Studio 26 (Standard) online in India from technology surface, you will be able to avail a whole host of different benefits. The first benefit is the fact that our relationship with customers doesn’t just persist until the sale lasts. Instead, we at technology surface have dedicated customer support services that are always ready, willing, and able to help you with any concerns and questions you may have about your software.
Symantec Academic & Non-Profit licenses are for sale to K-12 Schools, Community Colleges, Universities, IRS 501c3 Non-Profit Organizations and Churches in the US only.
1-Year Subscription License
Symantec Ghost Solution Suite is an industry leading and award-winning solution for deploying and managing desktops, laptops, tablets, and servers. From a single management console, you can quickly and easily migrate to the latest operating systems, inventory machines, deploy software, and perform custom configurations across multiple hardware platforms and OS types including Windows, Mac, and Linux.
Easy to use Management Console
With Symantec Ghost Solution Suite 3.3 you can do everything you need to manage your systems to manage your systems from within a single console without leaving your desk. Use the intuitive and fast interface to build jobs to perform all of your computer management tasks. A single job can include every step needed to provision and manage a machine, including disk configuration, OS deployment, network configuration, and software deployment.
Simplified Inventory, Software, and Settings
OS deployment and configuration is only part of the battle. Once a computer is in day-to-day usage, ongoing tasks like inventory, software management, and basic asset management are also important areas that must be addressed.
Symantec Ghost Solution Suite 3.3 makes it fast and easy to deploy, configure, and upgrade software on managed devices including being able to group machines based on application versions for easy targeting.
Symantec Ghost Solution Suite also enables power users to perform advanced automation and customized scripting. Whether it is support for server-side scripting or conditional error handling, Ghost Solution Suite provides nparalleled job and task management.
Technician’s Web Console
Symantec Ghost Solution Suite 3.3 includes a web-based console designed specifically for technicians with minimal experience. It complements the full console and is simple to use with built-in wizards for common tasks such as Windows 10 migration and image deployment. The console also has a modern UI and works with any browser.
With the web console, frequently run jobs can be delegated to frontline technicians to optimize resources and reduce costs. The web console is also highly scalable, so a large number of technicians can use it simultaneously.
Quick Tasks
Quick tasks allow you to schedule existing jobs, move computers to groups or to add new computers for immediate provisioning of images. Quick tasks can simplify complex processes into step-by-step flows that will make even the newest admin feel like a pro.
Job Creation Wizards
Job Creation Wizards provide step-by-step guides to create the most common jobs executed in the console. These wizards allow users to quickly learn how to create jobs and ensure consistency throughout the process. Jobs can be deployed using the web console and can also be edited further in the standard Symantec Ghost Solution Suite console.
Faster Imaging
A significant part of the time required for imaging machines is booting into automation. The longer a machine takes to get into automation, the longer the overall imaging process takes. Symantec Ghost Solution Suite 3.3 supports iPXE which delivers a dramatic speed improvement to the pre-boot automation process. iPXE shortens the overall downtime during deployment activities and gets the end user back to productivity quicker
Sophos Central Intercept X Advanced is a combination of Sophos Central Endpoint Protection and Intercept X products.
With Sophos Central Intercept X Advanced, you get all the features of Sophos Central Endpoint Protection and Intercept X in one product.
On the one hand, you benefit from great functions such as "Peripheral Control" or "Malicious Traffic Detection", and at the same time you get a specialist on your computer with Intercept X, which uses a technology called "CryptoGuard" to detect as soon as malware tries to encrypt files on your computer and stops this process immediately. Files that have already been encrypted are then automatically restored, so there is no data loss.
Would you like to see the Sophos Central user interface live? Just go to central.sophos.com and use the demo account. Username: demo@sophos.com / Password: Demo@sophos.com
Preventing the exploitation of security vulnerabilities.
Sophos Exploit Protection is a unique technology in Intercept X that prevents previously unknown or unpatched vulnerabilities in applications or operating system components from being exploited. With Intercept X, every application is monitored in the background and every action is checked to see if an exploit technique is being attempted.
If such a technique is detected, Exploit Prevention prevents a vulnerability from being exploited and restores the system to a secure state.
Find out the cause of the attack.
Imagine that, despite all the protective measures, malware has made it into your network. How could this happen? Thanks to the root cause analysis in Intercept X, this mystery can be uncovered with an impressive 360-degree analysis. The Root Cause Analysis Tool can tell you in great detail how the malware got into your network, which devices were infected and what steps you should take now.
With root cause analysis, you'll never be in the dark again if your network has been infected by an unknown malware.
Restores the system to its original state after an attack.
With Intercept X, thanks to technologies like CryptoGuard, you are protected against signatureless malware, such as ransomware, but after an attempted attack, your system still needs to be cleaned of all remnants. Since there is no cleaning routine for unknown malware, the entire processes of the executed malware must be forensically examined. This task is performed by Sophos Clean.
Sophos Clean performs a complete cleaning of the system after an attack has been stopped. It not only removes the malware itself, but replaces infected Windows resources with more secure original versions and ultimately restores the system to its original state, as it was before the infection.
Compare the feature set of Sophos’s various endpoint products to protect your clients. Not sure which protection best suits your business? We advise you free of charge and completely without obligation.
Explore our award-winning security features that provide complete protection against today’s dynamic threats for all your devices. Security and Privacy – For you and your family!
Provides complete protection to your important data against critical ransomware attacks. It detects and blocks unknown ransomware attacks in real time backed up by Behaviour Detection Technology.
Scans Wi-Fi router that your computer connects to and helps you know if the router is susceptible to vulnerabilities like DNS hijacking, weak password, or weak Wi-Fi encryption and recommends security measures.
Efficiently prevents programs called keyloggers from recording what you type on your keyboard while you are doing online banking or shopping or simply browsing the Internet.
Quick Heal DNAScan technology detects and blocks unknown threats. It uses a combination of behavioral and characteristic inspection and monitoring of unsafe programs.
Offers a number of scan options. You can scan on demand, schedule regular scanning, or scan certain file and folders.
Blocks viruses and malware that may infiltrate through external drives including CDs, DVDs, and USB-based devices.
Firewall blocks external threats that try to reach your computer over the Internet. It also blocks threats that may arise within networks that are connected to your system. Besides allowing you to configure protection for incoming and outgoing Internet traffic, our enhanced Firewall lets you set a Firewall profile for network connections such as ‘Home’, ‘Work’, ‘Public’ or ‘Restricted’. Stealth Mode is an added benefit. It hides your PC from the prying eyes of hackers.
The operating system (OS) settings and other applications in your system might have security vulnerabilities or weaknesses. Leaving these vulnerabilities unpatched can let hackers hijack your computer and data. Vulnerability Scan helps you detect such weaknesses. The feature also helps you fix vulnerabilities that could be present in the OS settings.
Ever vigilant, Virus Protection keeps scanning your files, documents, and system folders for malware or virus. Any new file is scanned without exception.
Prevents users from accessing phishing and fraudulent websites. Such websites lure you to share data with the hackers who can misuse to their advantage.
Suppresses prompts and notifications from Quick Heal for uninterrupted PC usage. This does not affect the security level of your system.
Efficiently blocks emails that might carry infected attachments or links to compromised or fake and phishing websites.
Scans registry, files and folders thoroughly to detect and clean spyware, adware, rogueware, dialers, riskware and many other potential threats in your computer.
Scans objects such as running processes, Windows registry, and files and folders for any suspicious activity and detects rootkits without any signatures.
Helps you restore the default settings of Internet Explorer modified by malware, spyware, or even by you.
Allows you to diagnose the computer system for any new malware or riskware and resolve the issues.
This facility stops unauthorized users from changing Quick Heal security settings when the system is running on Safe Mode.
Scans external drives automatically as soon as they are plugged into your computer for malware or virus.
Blocks copying of data from your computer to unauthorized USB drives.
Prevents unwanted intrusion attempts or attacks by hackers.
Allows you to restore critical system registry entries and other areas from the changes made by malicious programs. It also repairs the system registry.
Automatically detects unsafe and potentially dangerous websites and prevents you from visiting them.
Scans files and folders in lesser time without using too much system resources.
Stops autorun malware of the USB drive to curb spread of malware to your computer.
Ransomware Protection provides an additional layer of protection by supporting automatic smart backup that saves you from losing any important data in case of a ransomware attack. The feature automatically creates a backup of all your important files and also allows copying of backup to external device, for easy restoration even if your system gets compromised.
You can export Quick Heal security settings from a single computer and import it to other computers. This is helpful in cases where reinstallations or multiple computer configurations are concerned.
Protects your PC against spyware, adware, keyloggers, riskware, and other malicious programs.
Clean tracks of the files and documents that you work on to prevent privacy breach.
Register for our free TrackMyLaptop service and track your laptop if it gets lost or stolen. The service comes with every desktop product of Quick Heal at no extra cost.
Kindly note that, Quick Heal users have to register their Quick Heal Product License key at the TrackMyLaptop portal to avail this facility. Non-Quick Heal users have to register their Laptop's MAC ID. To know more, visit http://www.trackmylaptop.net/.
This is a free portal where you can add your Quick Heal enabled device, view its current status, and get notified of any critical situation such as malware infections. You can also renew your subscription via the portal. Visit Quick Heal RDM here.
Protects Quick Heal's running processes and services.
Microsoft Project Server 2019 is the penultimate version
of the proven server-based tool for project and portfolio management. The
latest version is Microsoft
Project Server Subscription Edition. As with Project Server 2016, the 2019 version and subscrition edition are a
feature of Microsoft SharePoint. You will install SharePoint and activate
Project Server after purchasing the licenses.
Microsoft
Project Server 2019 is the
penultimate version of the proven server-based tool for project and portfolio
management. The latest version is Microsoft Project Server Subscription
Edition. As with Project Server 2016, the 2019 version and subscrition edition
are a feature of Microsoft SharePoint.
Microsoft
Project Server is an on-premise project management and collaboration platform
that provides
a wide range of traditional and agile project management features. It allows users to manage projects, resources,
and portfolios with the help of powerful tools such as Gantt charts,
dashboards, and reports.
Functions
of Microsoft Project Server 2019
Project Server 2019 is a copy of Project
Online as of May 2018. The additional features in Project
Server 2019 compared to version 2016 are:
·
Team
Tasks can be accepted by several resources
·
Configurable
granularity (days, weeks, months, fiscal periods) of the Timephased Data in the
reporting database
·
More
settings for email notifications
·
Unique
project IDs when creating projects
·
450
custom fields and lookup tables
·
Resource
Engagement API available
Microsoft's new Windows Server 2022 Standard is ideal for small-to-medium-sized businesses that operate in physical or minimally virtualised environments. The license is core-based, so you must cover each physical core on the CPU. This product allows for the licensing of up to 16 cores. You also need a Client Access License (CAL) for each client that accesses Windows Server Standard edition.
Windows Server 2022 offers a wealth of new security features against advanced threats for physical servers. The baseline requirements for the hardware have been raised in order for Microsoft to be able to guarantee the higher level of protection. Improvements to Windows containers, better Azure integration, enhanced scalability, and more await you with Server 2022 Standard.
► Better security with Secure Core Servers - To counteract the rise of firmware attacks, Microsoft is taking full advantage of the tech incorporated into newer devices. HVCI, Boot DMA Protection, System Guard, Secure Boot, VBS, and TPM 2.0 all contribute to a trusted hardware platform that supports features such as full volume encryption, protection against credential attacks, Secure Boot and more.
► Enhances Azure integration - Experience a more integrated Azure with Windows Server 2022. Installing updates is also made easier with Hotpatch. Enhancements to Storage Migration Service make migrating storage to Windows Server or to Azure from more source locations easier.
► An improved Windows Admin Center - Enjoy faster startup thanks to a simplified Windows Container experience with Kubernetes that includes support for host-process containers for node configuration, IPv6, and consistent network policy implementation with Calico. Windows Server 2022 now supports business-critical and large-scale applications, such as SQL.
► Nested Virtualization for AMD processors - Run Hyper-V inside of a Hyper-V virtual machine and take advantage of more choices for hardware for your environments.
► 2 Virtual Machines - Additionally to the basic Windows Server 2022 functionalities, Windows Server 2022 Standard can run two operating system environments or virtual machines.
► Single Storage Replica - Standard edition supports limited Storage Replica feature with a 2 TB volume.
Read more in our blog article "Windows Server Editions Comparison".
The initial activation of all purchased products should be performed no later than 3 months after the purchase date. Note that the initial activation period is not the warranty period of the product - all warranty details are thoroughly explained in the terms and conditions section.
‣ Required Processor: 1.4 GHz 64-bit EMT64 or AMD64 processor required. The processor must support NX and DEP, CMPXCHG16b, LAHF/SAHF, and PrefetchW, as well as Second Level Address Translation (EPT or NPT)
‣ Recommended Memory: 512 MB (2 GB for Server with Desktop Experience installation option)
‣ Required Hard Disk Space: 32GB free space
‣ Required Display: 1024 x 768 screen resolution or higher
‣ Required Graphics Card: DirectX 10 graphics processor or higher
‣ Required Connectivity: Internet access (fees may apply); Network adapters on your PC should have a 1 gigabit per second ethernet adapter and be PCI compatible.
‣ Other: Trusted Platform Module 2.0 (TPM); UEFI 2.3.1c-based system and firmware that supports the Secure Boot feature.
If you have any further inquiries please do not hesitate to contact us!
Unleash your creativity and maximize productivity with QuarkXPress, layout, and desktop publishing software for print and digital design.
Whether you’re an independent designer, an international publisher, a student, or a business user, you can deliver every project on time and within budget with QuarkXPress – from newspapers and magazines to websites and e-books.
QuarkXPress capabilities
· Page Layouts - Produce stunning page layouts for any medium.
· Graphics & Illustrations - Refine graphics and illustrations on the digital canvas.
· Photo Editing - Correct, enhance and fine-tune images right up to the deadline.
· Digital Publishing - Convert print publications to responsive digital layouts, with no HTML-coding skills required.
With all these capabilities within QuarkXPress, you can say goodbye to the frustration of switching back and forth between different applications as deadlines loom.
Since 1981, we’ve been pioneers in desktop publishing and design for print and digital publishing. Today, with the world’s most powerful page layout and digital publishing software at your fingertips, your ideas become compelling visual realities.
Produce gorgeous print publications, large documents, and flex websites among many other content experiences.
System Requirements
· macOS 14.x (Sonoma)
· macOS 13.x (Ventura)
· macOS 12.x (Monterey)
Support
Access the Quark Knowledge Base and product documentation here - https://www.quark.com/support
Pricing
QuarkXPress is available as a monthly or annual subscription that renews automatically unless you cancel it at least 24 hours before it expires.
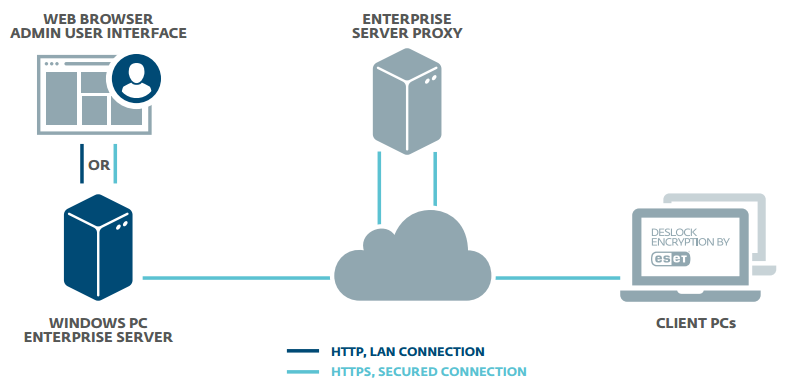
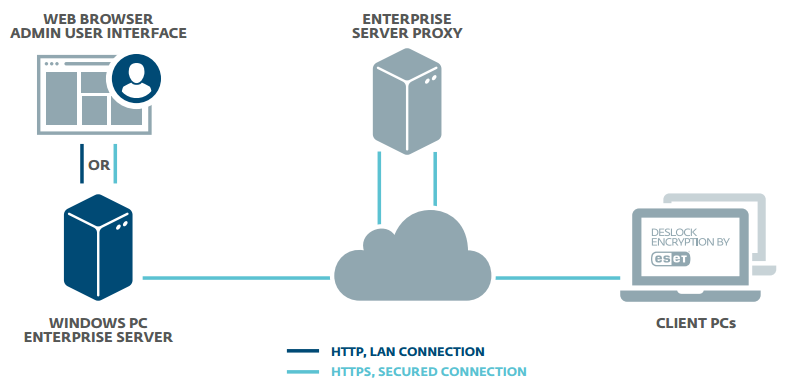
Endpoint Encryption by ESET is a simple-to-use encryption application for companies large and small. Take advantage of the optimized setup that speeds up the time to adoption for admins. The client side requires minimal user interaction, increasing user compliance and the security of your company data.
Do you do business in the European Union? The EU's General Data Protection Regulation (GDPR) comes into force in May 2018, and introduces significant new penalties for organizations that fail to protect their users' data adequately. One proven solution for data protection is encryption.
Data is a critical part of every organization, but this most valuable asset often poses a huge risk when it travels or is transmitted beyond the corporate network. Full disk and removable media encryption protect laptop computers against the unexpected. File, folder and email encryption allow fully secure collaboration across complex workgroups and team boundaries, with security policy enforced at all endpoints by the Endpoint Encryption+ Enterprise Server. Meet your data security compliance obligations with a single MSI package.
The Endpoint Encryption+ Enterprise server can manage users and workstations together or independently. Activation, and changes to security policy, software feature-set, encryption keys and endpoint status are all handled, securely through the cloud keeping your most high-risk endpoints under close control at all times Home and mobile working make extending encryption security policy beyond the perimeter of your network a necessity. Only Endpoint Encryption+ offers full control wherever your users are.
If you want to create or work with PDF files, then you may want to buy NITRO PDF PRO online right now. NITRO PDF PRO is the type of tool designed to really bring you the efficiency and help that you need at the highest possible level. The true focus is on value and professionalism, and you also get to ensure that you create and edit, convert PDF files and also keep them secure at all times. It’s a clever idea that works very nicely, and you will be impressed with the versatility and value of these files.
On top of that, with NITRO PDF PRO, you can finally ensure that you use this for all your business needs. You can buy NITRO PDF PRO in India right now and that alone can help eliminate concerns and push the limits in a creative manner. That alone really helps add up to the process and convey a stellar value and benefits all the time.
With that being said, you will notice that the NITRO PDF PRO solution is very detailed, professional and it definitely gets the job done very nicely. Plus, this is a great tool you can use to edit and also create the PDF files you want. The drag and drop system make everything very intuitive and you don’t have to worry that anything is misplaced. In case it is, you can always edit and modify the file as you see fit.
And that’s where a tool like NITRO PDF PRO shines, because it helps convey great value and quality, and it also offers you much better security too. Thanks to the necessary security, everything works as expected and you don’t need to worry about anything. The file can be accessed the way you want, without worries or dealing with challenges. And that’s where everything really shines and stands out, because it does convey the benefits and solutions you may need.
Create PDFs and Combine Files | |
Convert Files to and from PDF | |
Edit PDF files | |
Review, Markup, and Annotate PDFs | |
Build and Fill PDF forms | |
Keep PDFs secure | |
Digitally Sign and Certify Documents | |
Cloud storage integrations | |
Customizable Ribbon Tab | |
Microsoft Office-like interface | |
Community Forum | |
On-boarding videos & articles |
What do you need when you need to acquire a PDF editing or creating solution for professional use? This is the perfect time to buy NITRO PDF PRO online in India. This helps you create PDF files fast and easy, and you will appreciate just how fast it is to work with such a tool. The fact that you don’t have to waste any extra time and you just get the job done fast is exactly where a tool like this shines every time.
Whenever you buy NITRO PDF PRO online in India, you don’t have to worry about licensing or problems like that. It’s just a more professional solution, it gets the job done, and in the end everyone wins. That’s the thing that matters here, and if you do it right, nothing stands in your way. The best part is that you get to choose the license you need, you can even go for a team license too, and that alone always helps you do business properly.
Plus, with the NITRO PDF PRO tool, you can ensure that all the PDF files you create or share are very secure. It really eliminates concerns and that always helps push the limits in a very creative and enjoyable manner. That alone always helps and the best approach is that it brings in front a much better set of benefits.
Explore our award-winning security features that provide complete protection against today’s dynamic threats for all your devices. Security and Privacy – For you and your family!
Get real time, easy-to-understand visual snapshots of your digital wellbeing reports, along with recommendations to improve your digital safety and online privacy.
Endpoint Encryption by ESET is a simple-to-use encryption application for companies large and small. Take advantage of the optimized setup that speeds up the time to adoption for admins. The client side requires minimal user interaction, increasing user compliance and the security of your company data.
Do you do business in the European Union? The EU's General Data Protection Regulation (GDPR) comes into force in May 2018, and introduces significant new penalties for organizations that fail to protect their users' data adequately. One proven solution for data protection is encryption.
Data is a critical part of every organization, but this most valuable asset often poses a huge risk when it travels or is transmitted beyond the corporate network. Full disk and removable media encryption protect laptop computers against the unexpected. File, folder and email encryption allow fully secure collaboration across complex workgroups and team boundaries, with security policy enforced at all endpoints by the Endpoint Encryption+ Enterprise Server. Meet your data security compliance obligations with a single MSI package.
The Endpoint Encryption+ Enterprise server can manage users and workstations together or independently. Activation, and changes to security policy, software feature-set, encryption keys and endpoint status are all handled, securely through the cloud keeping your most high-risk endpoints under close control at all times Home and mobile working make extending encryption security policy beyond the perimeter of your network a necessity. Only Endpoint Encryption+ offers full control wherever your users are.
Microsoft Office LTSC (Long Term Servicing Channel)
Professional Plus 2021 is a perpetually licensed version of Microsoft Office that
allows users to install a collection of software developed by Microsoft for
productivity, collaboration, cloud storage, and more. Microsoft supports each LTSC release for five
years.
Microsoft has maintained the major version of Office LTSC 2021 as 16.0. This version is the same as Office 2016 and Office 2019, ensuring policies and registry settings can reference the exact location.
Exchange 2019 is the email, contact, calendaring,
scheduling, and collaboration platform powered by Windows Server. The Enterprise edition's security and performance
enhancements ensure improved search infrastructure, plus faster and more
reliable failovers. Other n. Up to 100 mailbox databases.
Provides support for up to 256 gigabytes (GB) of memory and
48 central processing unit cores. Enables installations on Windows Server Core.
Enables external access to Exchange admin center and Exchange Management Shell
to be blocked natively.
Feast your eyes on vibrant, super-sharp 4K High Dynamic Range visuals4 that bring breathtaking virtual reality environments into clear focus.
Revel in imagery of superior quality as two 2000 x 2040 OLED displays deliver over four times the resolution generated by the original PlayStation VR headset for a comfortably smooth visual experience at up to 120fps.
Play with freedom and experience different VR play styles, as PlayStation VR2 tracks you and your controllers through four cameras embedded in the headset.
Your movements and what you look at is reflected in-game, without the need for an external camera.
Discover rich emotional experiences as you interact with the game world and other players.
Eye tracking cameras detect when your eyes are open and track their movements and the emotions they convey – which can be reflected through in-game situations.1
When combined with your headset and controllers’ positions and actions, this allows you to fully express yourself and communicate with others in online multiplayer2 in exciting new ways.
Eye tracking also follows your line of sight when aiming or looking around, and advanced foveated rendering techniques improve the visual experience by adjusting resolutions to pinpoint and enhance whatever you’re focusing on.
